Hybrid Cloud — The Challenge of Exploration
The COVID-19 (or Coronavirus) epidemic has caused a global event with far-reaching consequences that go beyond healthcare. It’s radically altering how businesses and IT departments operate.
It would be ideal if we could lay out a single set of instructions that would work perfectly in any case, but environments come in a variety of shapes and sizes. Perhaps more diverse are the number and types of applications hosted within these various environments.
For support staff who deal with these applications on a regular basis, the variety of applications and possible problems keeps things exciting. This diversity and possible infrequency of contact can be a problem if you’re in charge of making strategic decisions for an organisation.
When faced with a problem like this, it’s a smart idea to start collecting data and letting the data lead the way.
Set the Assessment
Series I—Gathering Business Data
You’ll want to speak with business stakeholders, application owners, and end users during the first step to figure out which business functions are served by which applications, as well as their relevance to the company.
Take the time to learn about the users’ workflows and how the applications in your system communicate. After all, departments and teams are not islands, and the performance of one often serves as an input for the work of another.
These are only a few examples, but the aim is to get a deeper understanding of how things function at a business level and how people in the company use technology to carry out their job responsibilities.
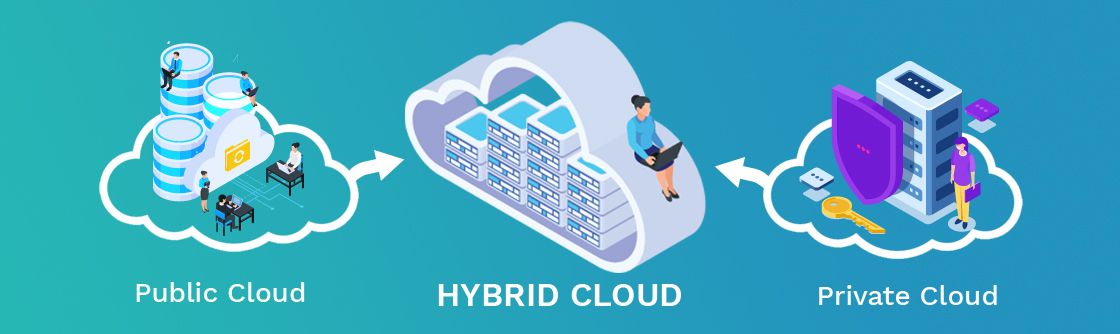
As you’ll see, identifying an application’s purpose and value, the effect of downtime, input and output processes, and end-user position are all important factors in deciding where an application belongs in your future-state hybrid architecture.
As you’ll see, identifying an application’s purpose and value, the effect of downtime, input and output processes, and end-user position are all important factors in deciding where an application belongs in your future-state hybrid architecture.
Series II—Collecting technical data
We’ll try to gather technical detail in the second step to fill in the gaps and back up the details we gathered during our business-level evaluation.
Begin by creating a list of physical and virtual systems, making sure to provide information such as the device name, IP address, resource allocations, operating system, and running applications. Analyze this data and make a list of which roles the device performs and which applications it serves.
Take advantage of the opportunity to examine the systems’ contact patterns as well. This could include integrating all systems into an existing monitoring solution or creating a new tool just for this reason.
This will show you how an application’s levels communicate and where user contact originates. You’ll also notice proof of the collaboration between the teams and applications you found in the first phase.
You may need to pause, take ten deep breaths, and calmly ask yourself why the previous admin or architect enabled ONE device to be a single point of failure AND performance bottleneck for multiple business-critical applications as you bring this information together.
Take comfort in knowing that all is now in your control! The only way out of this situation is with a methodical and systematic approach, as well as an amount of information.
Now that you have a clear understanding of resource needs, dependencies, and traffic trends, you can think about the effect a possible application relocation will have on the business’s operations.
The effort that went in here would pay off in the later stages of the transition, such as migration and ongoing management.
Series III—Map and Synchronization
You’ve learned about the specific applications used by your company, who uses them, and which underlying software and hardware components support them at this stage. You’re in a much better place to start making choices now.
Going a step further and combining this business and technological data into a single spreadsheet or even a set of diagrams can be extremely beneficial. You can need to back up your decisions later or else present the current situation in a way that businesspeople will understand.
This will be an excellent way to solve the issue and find acceptance for your strategy and design. Plus, short of having a wall of CLI windows open on your screen, there’s no better way to feel like a “pro” than spending hours perfecting a diagram.
The application’s implementation
Why are they going about things the way we are? Isn’t it true that a changed procedure will be more efficient?
What is the point of having this application? Isn’t a managed service offering a stronger and more cost-effective option?
Is it just my imagination, or is that Windows Server 2003?!
If we’re going to put effort into replatforming our apps, it would be a good idea to take a step back and justify our application use first, as the two go hand-in-hand.
After all, why build a beautiful, modern technological infrastructure to sustain an application that will be replaced anyway?
SMAC Tech Responds With DevOps Tools Integration on a Hybrid Cloud to Track, Manage, and Secure IT Environments Remotely.
SMAC Tech is aware of the unexpected challenges that IT professionals are facing as a result of the COVID-19 outbreak.
We’re expanding full remote support to help the IT pro community rapidly respond to the needs of their end users. Our Automation remote support will enable your business to connect to global customers and provide them with stable support.
Moving Forward Together
We will continue to search for ways in which SMAC Tech Labs can assist organisations in addressing these issues, and where we can collaborate creatively to solve problems.
CATEGORIES
- SEO (6)
- Social Media (3)
- Web Development (14)